SentinelOne
Founded Year
2013Stage
IPO | IPOTotal Raised
$799.52MDate of IPO
6/30/2021Market Cap
5.70BStock Price
17.85Revenue
$0000About SentinelOne
SentinelOne focuses on autonomous security solutions. It offers a platform that unifies prevention, detection, response, remediation, and forensics for endpoint, cloud, and identity environments. Its platform uses artificial intelligence to provide real-time protection and automated response capabilities against known and unknown threats, including malware, ransomware, and advanced persistent threats. It was founded in 2013 and is based in Mountain View, California.
Loading...
ESPs containing SentinelOne
The ESP matrix leverages data and analyst insight to identify and rank leading companies in a given technology landscape.
The vulnerability management market helps organizations identify and prioritize vulnerabilities in their IT systems, networks, and applications to reduce the risk of cyberattacks and data breaches. Companies provide insights into potential security gaps with guidance on remediation, often featuring automated security validation, threat intelligence integration, and real-time vulnerability detectio…
SentinelOne named as Highflier among 15 other companies, including Google Cloud, Accenture, and Amazon Web Services.
Loading...
Research containing SentinelOne
Get data-driven expert analysis from the CB Insights Intelligence Unit.
CB Insights Intelligence Analysts have mentioned SentinelOne in 5 CB Insights research briefs, most recently on Oct 30, 2025.
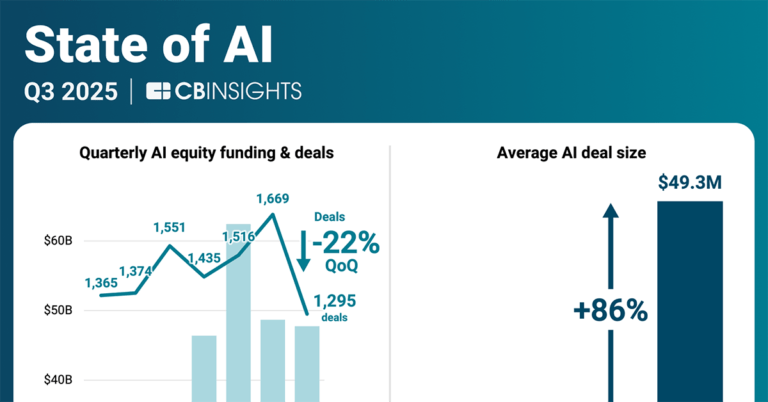
Oct 30, 2025 report
State of AI Q3’25 Report
Nov 3, 2023
The endpoint security market map
Jul 28, 2023
The cloud security market mapExpert Collections containing SentinelOne
Expert Collections are analyst-curated lists that highlight the companies you need to know in the most important technology spaces.
SentinelOne is included in 6 Expert Collections, including Tech IPO Pipeline.
Tech IPO Pipeline
568 items
AI 100 (All Winners 2018-2025)
200 items
The winners of the 4th annual CB Insights AI 100.
Cybersecurity
11,390 items
These companies protect organizations from digital threats.
Fintech
9,809 items
Companies and startups in this collection provide technology to streamline, improve, and transform financial services, products, and operations for individuals and businesses.
Advanced Manufacturing
7,014 items
Companies in the advanced manufacturing tech space, including companies focusing on technologies across R&D, mass production, or sustainability
Artificial Intelligence (AI)
20,629 items
SentinelOne Patents
SentinelOne has filed 13 patents.
The 3 most popular patent topics include:
- computer network security
- computer security
- computer memory

Application Date | Grant Date | Title | Related Topics | Status |
|---|---|---|---|---|
2/23/2023 | 3/25/2025 | Computer memory, Directory services, C libraries, Computer security, Computer network security | Grant |
Application Date | 2/23/2023 |
|---|---|
Grant Date | 3/25/2025 |
Title | |
Related Topics | Computer memory, Directory services, C libraries, Computer security, Computer network security |
Status | Grant |
Latest SentinelOne News
Nov 3, 2025
A new way to think about zero trust for workloads Static credentials have been a weak point in cloud security for years. A new paper by researchers from SentinelOne takes direct aim at that issue with a practical model for authenticating workloads without long-lived secrets. Instead of relying on static keys, the team proposes using temporary, verifiable tokens that expire within minutes. Breaking from static credentials The researcher’s core argument is that static keys are incompatible with zero trust. These credentials often last months or years, and if stolen, they can give attackers broad access to cloud resources. In multi-cloud settings, this becomes even harder to manage. Each static key adds to the operational load of rotating, auditing, and securing thousands of secrets that can be reused across environments. The researchers built and tested their model in a large enterprise environment that spans more than 100 Kubernetes clusters and multiple public clouds. Their system replaces static credentials with short-lived, cryptographically signed tokens that workloads use to prove their identity to other systems. Chris Boehm , Field CTO at Zero Networks, told Help Net Security that the concept aligns with how CISOs should approach zero trust in practice. “If I were advising a CISO, I would tell them to start with visibility. You must know every workload and understand who or what communicates with it. Then reduce access to the minimum necessary and allow privilege elevation only through controlled and monitored actions,” Boehm said. A federated model built on open standards At the heart of their approach is Workload Identity Federation (WIF) and OpenID Connect (OIDC). Together, these technologies allow workloads to authenticate through trusted identity providers rather than storing credentials locally. In practice, this means a workload requests a signed JSON Web Token (JWT) from its environment’s identity provider. The token contains claims such as who issued it, who it represents, and who can accept it. When the workload presents this token to another cloud service, that service checks the signature and verifies that the token was issued by a trusted provider. If the verification passes, the cloud issues a temporary credential for that request. The token is short-lived and scoped to a specific purpose, so even if it were stolen, its value to an attacker would be limited. The researchers describe this as a federated approach, where identity and trust flow between clouds through established, auditable relationships. Each request is verified independently, which supports the zero trust principle of “always verify.” Tested at enterprise scale SentinelOne deployed this architecture in its own production environment, which includes workloads across AWS, Google Cloud, and Azure. Before adopting the federated model, the environment used thousands of long-lived keys for service accounts, user identities, and cloud applications. After the shift, those static keys were replaced with on-demand tokens that last less than an hour. This reduced the average credential lifetime by more than 99 percent and cut the burden of managing secrets across platforms. The team also reported an 80 percent drop in the time needed for compliance audits, since the trust model became centralized and easier to trace. For developers, provisioning secure cross-cloud access went from taking days to minutes. The system automatically enforces least privilege by using claims within each token to limit what the workload can do and for how long. Cutting risk through short-lived access The paper compares the risk models of static credentials and federated tokens. In the legacy model, overall risk grows with the number of keys, their long lifetimes, and the wide permissions they often carry. The new model changes that by reducing lifetime and scope. A token might exist for only 60 minutes and be tied to one workload or API. This lowers the “blast radius” of any single compromise. The authors show that by shifting from persistent credentials to ephemeral tokens, the operational complexity also drops. Instead of managing thousands of secrets, teams manage only a few trusted identity providers. This helps control costs by reducing manual work and limiting resource duplication. Built-in defenses against known threats The framework addresses several common risks. The “Confused Deputy” problem, where a service is tricked into misusing its authority, is prevented by the audience claim in each token, which ensures it can only be used by its intended target. The model also removes the need to store secrets in files or secrets managers, reducing the risk of leaks during credential distribution. For third-party integrations, trust can be created through federation with the vendor’s identity provider and revoked instantly if needed. This avoids the slow and uncertain process of rotating static keys. Continuous verification redefined One of the most important ideas in zero trust is continuous verification, which the SentinelOne framework supports by requiring every workload interaction to be reauthenticated. Boehm noted that this concept is often misunderstood. “Continuous verification should not mean more MFA prompts or stricter NAC rules,” he said. “Those are momentary checks that expire the second access is granted. True continuous verification comes from using behavioral and contextual signals such as process activity, communication patterns, and timing to reassess trust dynamically.” His point echoes the research’s focus on minimizing implicit trust at the workload level. The paper shows that by combining identity federation with short-lived tokens, each request becomes its own trust decision, based on fresh data rather than static credentials. The road toward dynamic authorization While the current work focuses on authentication, the authors see room for expansion. They propose linking this system to attribute-based access control (ABAC), where tokens could include contextual information such as project tags or workload metadata. This would allow access decisions to change dynamically based on attributes. They also mention the idea of “just-in-time” credential issuance, where a token would exist only for the duration of a specific task or job. That would further narrow the window for attackers to exploit stolen credentials . More about
SentinelOne Frequently Asked Questions (FAQ)
When was SentinelOne founded?
SentinelOne was founded in 2013.
Where is SentinelOne's headquarters?
SentinelOne's headquarters is located at 444 Castro Street, Mountain View.
What is SentinelOne's latest funding round?
SentinelOne's latest funding round is IPO.
How much did SentinelOne raise?
SentinelOne raised a total of $799.52M.
Who are the investors of SentinelOne?
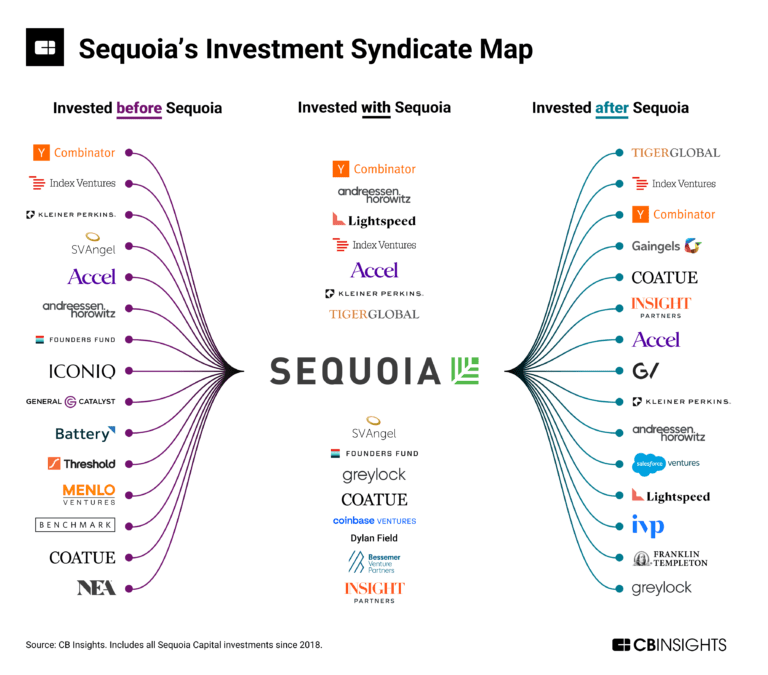
Investors of SentinelOne include Insight Partners, Tiger Global Management, Third Point Ventures, Sequoia Capital, Accel and 23 more.
Who are SentinelOne's competitors?
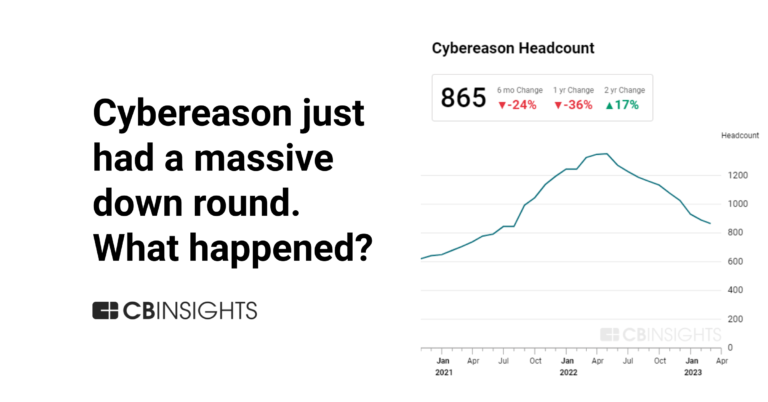
Competitors of SentinelOne include CloudWize, Cybereason, CyCraft, ThreatLocker, Unosecur and 7 more.
Loading...
Compare SentinelOne to Competitors

Darktrace provides a cybersecurity platform across various sectors. The company offers products that use artificial intelligence to detect and respond to cyber threats in real time, aiming to protect digital assets and organizational data. Darktrace's solutions focus on securing networks, emails, cloud environments, operational technology, identities, and endpoints from cyber threats. It was founded in 2013 and is based in Cambridge, United Kingdom.

Vectra AI operates in the field of Artificial Intelligence (AI) driven cybersecurity, in extended detection and response (XDR) within the cybersecurity industry. It provides a platform that integrates network, identity, cloud, software as a service (SaaS), and generative AI for security solutions. Its services aim to detect, prioritize, investigate, and respond to hybrid cyber-attacks, assisting security teams in protecting against various cyber threats. Vectra was formerly known as TraceVector. It was founded in 2011 and is based in San Jose, California.

Sophos provides cybersecurity solutions, including Managed Detection and Response, incident response, endpoint, network, email, and cloud security, aimed at protecting organizations from cyberattacks. The company serves various sectors by offering cybersecurity-as-a-service, security operations platforms, and hybrid solutions that can be managed directly by the organization or supplemented with additional services. It was founded in 1985 and is based in Abingdon, United Kingdom.

Bitdefender provides threat prevention, detection, and response solutions across various sectors. The company offers cybersecurity products and services for consumers, small businesses, and enterprises aimed at protecting against digital threats. Bitdefender's offerings include endpoint security, cloud security posture management, and managed security services, supported by AI-powered threat intelligence. It was founded in 2001 and is based in Bucharest, Romania.

SonicWall provides cybersecurity solutions that focus on breach detection and prevention for business networks. The company offers services that protect networks, emails, applications, and data from cyber threats. It was founded in 1991 and is based in Milpitas, California.

Tanium focuses on providing endpoint management solutions within the information technology (IT) security and management sector. Its main offerings include a platform that enables organizations to manage their IT lifecycle, assess risks and compliance, respond to incidents, and support digital employee experiences. Tanium primarily serves sectors such as federal, government, education, energy, financial services, healthcare, manufacturing, retail, and technology. It was founded in 2007 and is based in Emeryville, California.
Loading...